In the high-speed world of digital marketing, we often obsess over metrics that offer immediate gratification: open rates, click-through rates (CTR), and conversion percentages. We invest thousands of dollars in high-quality copywriting, behavioral triggers, and complex automation sequences designed to nurture a lead from awareness to purchase. However, there is a silent, invisible force that can dismantle even the most sophisticated marketing engine before it even gets started: Email Bounce Rates.
If your emails aren't reaching the inbox, your strategy isn't just failing—it’s actively costing you money. The problem in 2026 is that the definition of a "bad email" has evolved. Simple syntax checks are no longer sufficient. This is where UseBouncer.com steps in, moving beyond simple "list cleaning" to provide a comprehensive Email Deliverability Shield.
The Deliverability Death Spiral: Understanding Sender Reputation
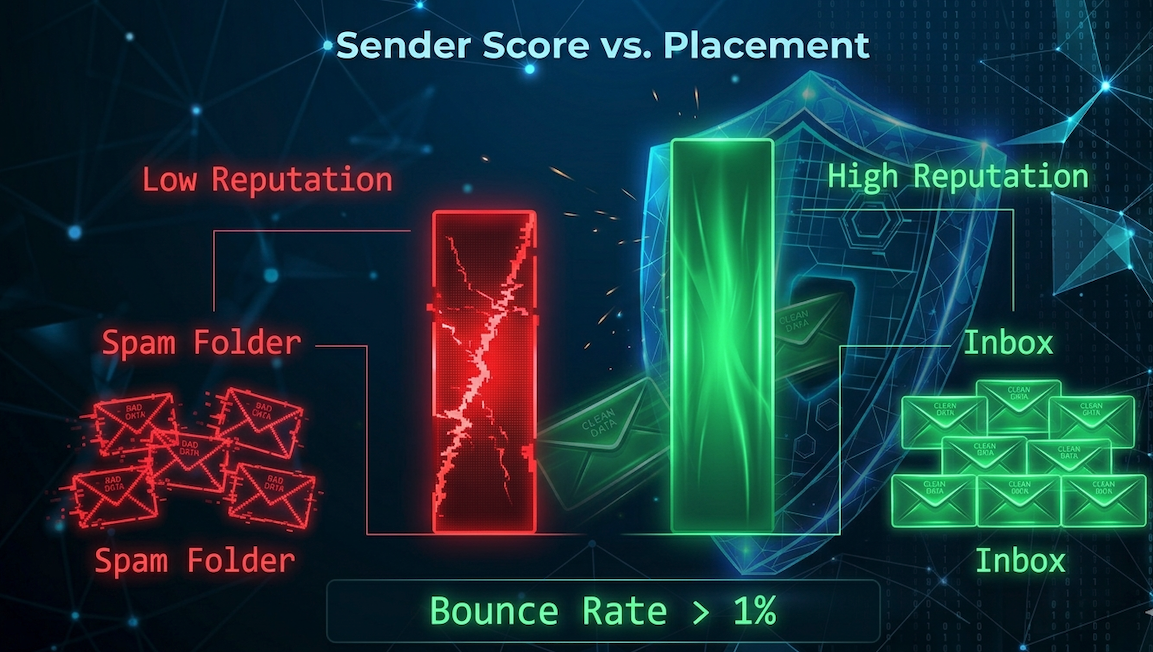
Many marketers treat a bounce rate of 2% or 5% as a minor nuisance—a cost of doing business. This is a fundamental misunderstanding of how modern Internet Service Providers (ISPs) like Gmail, Outlook, and Yahoo view sending behavior. In 2026, ISPs have become ruthless gatekeepers.
When you send an email, the receiving ISP assigns your domain and IP address a Sender Reputation Score. Think of it as a credit score for your email marketing. If you consistently send messages to non-existent, invalid, or "risky" email addresses, your reputation score plummets.
The Consequence of Apathy
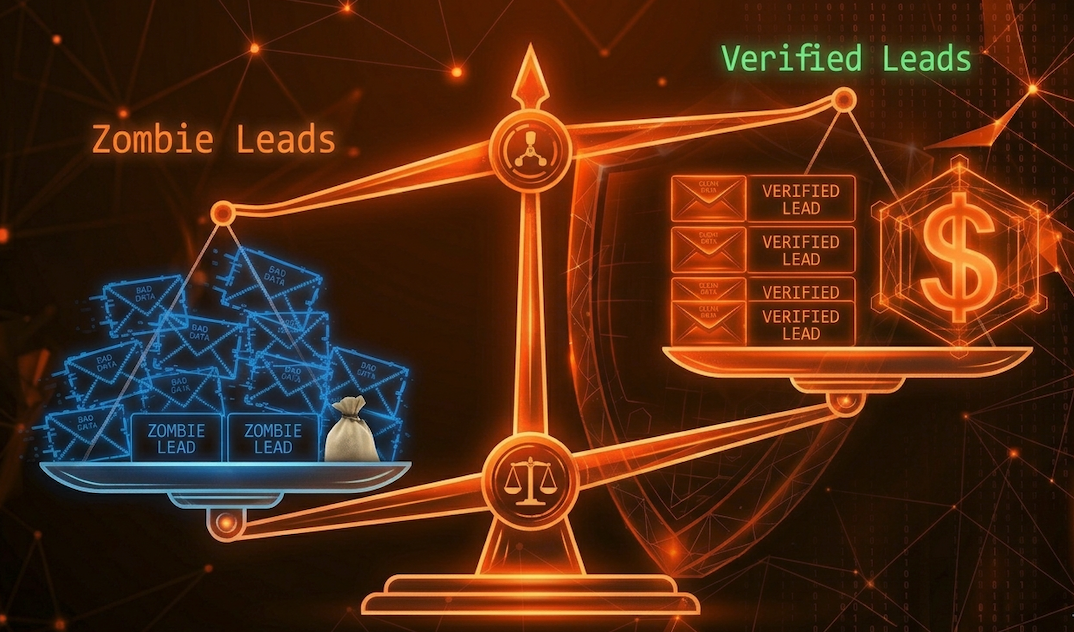
Once your reputation is tarnished, ISPs stop trusting your mail. The immediate result is that even your legitimate emails—the ones going to your most engaged customers—will start landing directly in the Spam Folder. This is the "Deliverability Death Spiral." You lose visibility, your engagement metrics crash, your ROI vanishes, and eventually, your domain might be permanently blacklisted by major providers, a catastrophic outcome for any modern business. UseBouncer acts as your digital gatekeeper, ensuring that only verified, "deliverable" addresses ever enter your active sending queue.
Beyond Syntax: The Advanced Science of Verification
A basic verification tool might check if an email has an "@" symbol or ends in ".com." That is elementary logic. UseBouncer’s engine performs a multi-layered, deep-dive analysis of every address:
- SMTP Validation: Bouncer communicates directly with the recipient's mail server. It initiates a "handshake" protocol (a conversation) to ask if the mailbox physically exists, all without actually sending a noisy message that would alert the user.
- Catch-All Detection: It identifies domains configured to accept all mail sent to any address, regardless of whether a mailbox exists. These "catch-all" or "accept-all" addresses are notoriously risky. Often, an ISP will accept the email initially to protect user privacy, only to secretly mark it as undeliverable or low-quality later. Sending to too many catch-alls will systematically degrade your sender reputation.
- Disposable Email Filtering: In an age of "freebie-seekers," many users sign up for newsletters or download lead magnets using "burner" email addresses (like
temp-mail.orgor10minutemail.com). These addresses expire after minutes or hours. UseBouncer flags these non-engaging addresses, keeping your list focused on genuine prospects.
Toxicity Check: Identifying the "Landmines"
The most dangerous emails aren't just "invalid" or "disposable"; they are toxic. A toxic email address is one that actively signals to an ISP that you are a spammer. This category primarily includes Spam Traps.
A Spam Trap (or Honeypot) is a legitimate-looking email address created by an ISP or a security organization specifically to catch "scrapers," "harvesters," and irresponsible marketers. These addresses are never used by a real human to opt-in to anything. If you hit a single Spam Trap, your deliverability can be throttled instantly, or your domain can be blacklisted. UseBouncer’s specialized Toxicity Check scans your list for these digital landmines, providing a layer of protection against domain-level damage that basic cleaners simply miss.
Privacy-First Architecture: Built for Global Standards
In 2026, data privacy is a primary concern for enterprise clients. UseBouncer isn't just a powerful tool; it is a compliant one. The architecture is designed around GDPR and other strict global data protection regulations. When you upload a list to UseBouncer, you are using a hashed, secure processing method. Your sensitive customer data is never stored longer than necessary, and it is handled with bank-level encryption. For enterprise senders, verification isn't just about deliverability; it's about maintaining a secure, compliant data supply chain.